Azure Key Vault Integration
An Azure Key Vault integration with Cloudhouse Guardian (Guardian) allows you to securely retrieve credentials (secrets) from your organization’s existing Azure Key Vault as an alternative to storing them directly within Guardian. To enable this, add an Azure Key Vault integration to your Guardian instance by providing the Vault URL and the authentication details required to access the stored secrets.
Once you have added an Azure Key Vault integration, Guardian can retrieve secrets from the configured vault(s) and make them available for selection when you add Windows, Linux or Network device nodes. These secrets are then used to authenticate access to nodes during scans. This topic describes how to set up an Azure Key Vault integration with Guardian.
Note: This feature was introduced in V3.63.0 of the Guardian Web application. This is an optional feature that must be enabled. For more information on how to enable it, contact your Cloudhouse Representative.
Dependencies
To add an Azure integration, you need the following:
-
A Microsoft Azure account subscription.
-
Access to one or more Azure Key Vaults. Each Key Vault has a unique Vault URL; you can add one or multiple Vault URLs when adding an Azure Key Vault integration. For more information, see Add an Azure Key Vault Integration.
-
Ensure Guardian has access to that vault. To do this, you need to set up and configure a Microsoft Azure account with the correct permissions. For more information, see Microsoft Azure Account.
-
-
Azure Key Vault credentials have been created in Guardian. For more information, see Azure Key Vault Credentials.
Add an Azure Key Vault Integration
When adding an Azure Key Vault integration, you must specify add the authentication details and specify the Vault URL(s) to access the stored secrets, allowing Guardian to retrieve them and use them as authenticators during scans.
To add an Azure integration to Guardian, complete the following:
-
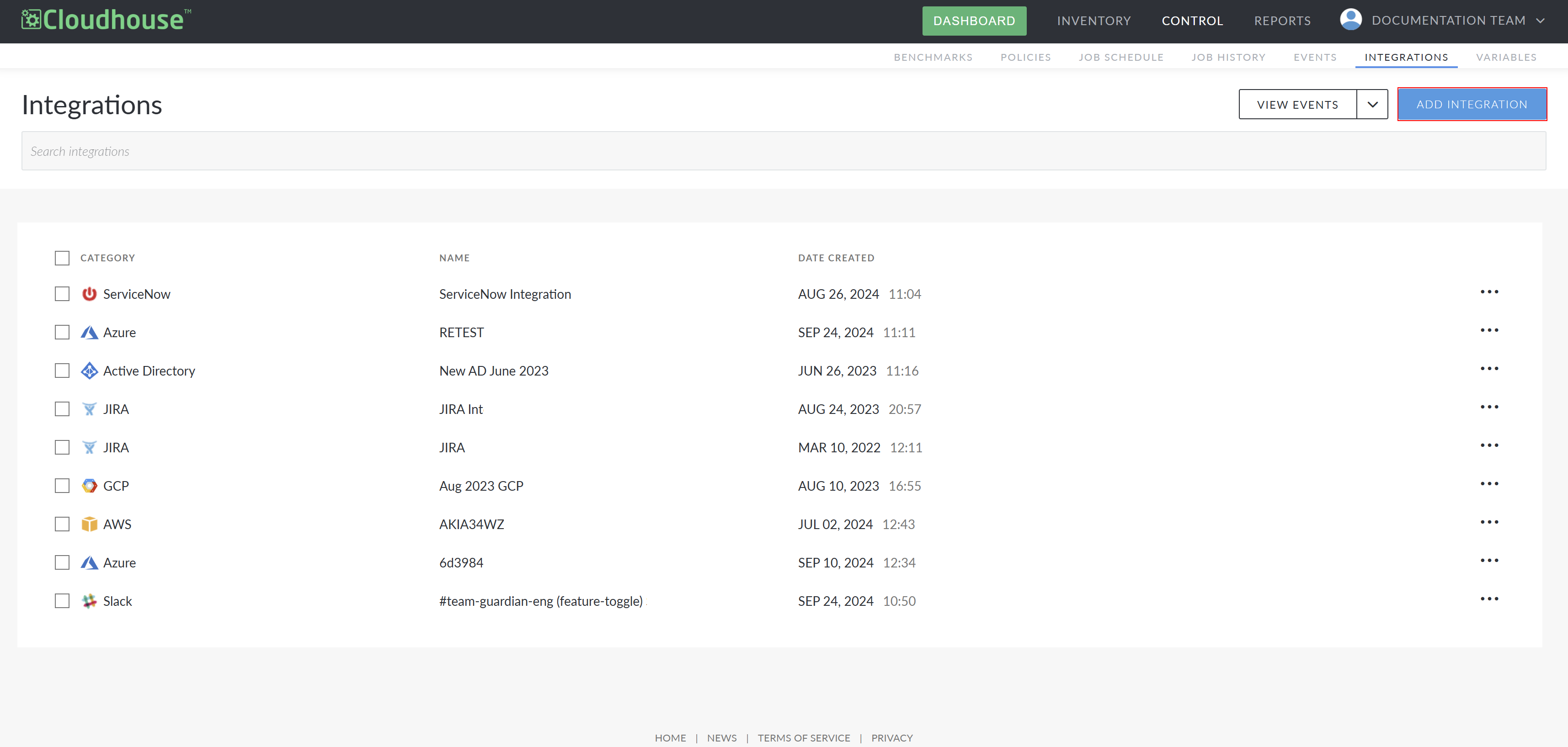
In the Guardian web application, navigate to the Integrations tab (Control > Integrations) and click Add Integration. The Add Integration page is displayed.
-
Select Azure Key Vault from the list of available integrations.
-
In the Name field, enter the display name for the integration within Guardian. This name is how you will identify the integration among all others configured in your Guardian instance, so ensure it is descriptive.
-
Select the one of the following credentials from the What Credentials Would You Like To Use? radio buttons:
-
Existing integration – Import credentials from an existing Azure integration. If selected, the Azure Integration credentials drop-down list is displayed. For more information, go to Step 5.
-
Manually enter credentials – Manually enter Azure credentials. If selected, the following fields are displayed. For more information, go to Step 6.
-
Connection Manager Group drop-down list
-
Subscription ID field
-
Tenant ID field
-
Client ID field
-
Client Secret field
-
-
-
If you selected the Existing integration radio button, complete the following options:
Note: If you selected the Manually enter credentials radio button in Step 4, go to Step 6.
Option
Description
Azure Integration credentials drop-down list A list of Azure integrations created in Guardian. Select an existing integration from the list, the Client Secret associated with the integration will define what credentials are available to use.
Vault URL field The URL of the Azure Key Vault whose secrets will be available when adding nodes. The URL can be sourced from the Azure portal. For example,
https://test-kv01.vault.azure.net/. You can also complete the following actions:-
Remove – Remove a Vault URL from the integration
-
Add Vault URL – Add another Vault URL if you have two or more Azure Key Vaults configured.
Once you have completed the options, go to Step 7.
-
-
If you selected the Manually enter credentials radio button, complete the following options:
Option
Description
Connection Manager Group drop-down list The Connection Manager group that is responsible for scanning and retrieving your Azure node(s). Select a Connection Manager group from the drop-down list.
Subscription ID field*
The unique alphanumeric string that identifies your Azure subscription. Enter an Azure subscription ID to include in the scan.
For more information on how to source the subscription ID, see Microsoft Azure Account.
Tenant ID field
The Globally Unique Identifier (GUID) that represents your Microsoft Entra ID (previously Azure Active Directory) instance. For more information on how to source this, see Microsoft Azure Account.
Client ID field
The unique identifier assigned to your application, registered within the Microsoft Entra ID (previously Azure Active Directory) instance. For more information on how to source this, see Microsoft Azure Account.
Client Secret field
The unique identifier that the application uses to prove its identity when requesting a token. For more information on how to source this, see Microsoft Azure Account.
Vault URL field The URL of the Azure Key Vault whose secrets will be available when adding nodes. The URL can be sourced from the Azure portal. For example,
https://test-kv01.vault.azure.net/. You can also complete the following actions:-
Remove – Remove a Vault URL from the integration
-
Add Vault URL – Add another Vault URL if you have two or more Azure Key Vaults configured.
-
-
Once you have set the correct values for each of the options displayed (dependent on the radio button you selected in Step 4), click Done to create the Azure Key Vault integration.
If successful, a confirmation message is displayed and the Azure Key Vault integration is added to the Integrations tab of your Guardian instance. If unsuccessful, an error message is displayed. Use the information displayed in the error message(s) to troubleshoot the values in your Azure Key Vault Integration options.
Troubleshooting
If you are experiencing issues with your integration, try the following:
-
Verify that the account credentials supplied for the integration are correct.
Azure Roles Based Access Control
A Global Reader role may be used to sync all supported Azure nodes. However, for more granular control, multiple Azure AD roles may be required. For more information, see Azure Roles Based Access Control.